Hey there! As a network security enthusiast who’s spent the last decade tinkering with home networks, I’ve seen it all – from smart fridges getting hacked to baby monitors being compromised. Pretty scary stuff, right? Here’s a mind-blowing stat for you: the average home now has over 25 connected devices! As someone who’s spent years implementing zero trust home network principles, I can tell you that each of those devices is a potential gateway for cyber criminals.and unfortunately, the old “lock the front door” approach just doesn’t cut it anymore.
You know what keeps me up at night? The thought that somewhere out there, someone could be trying to access my home network right now. But don’t worry! I’m here to share everything I’ve learned about creating a fortress-like home network using something called “zero trust” principles. Trust me, it’s not as complicated as it sounds!
Understanding Zero Trust for Home Networks
Remember when we used to think having a strong WiFi password was enough? Those were simpler times! But with the rise of smart home devices and remote work, our home networks have become as complex as small business networks. I learned this the hard way when my “super-secure” network got compromised through – get this – my smart garage door opener!
Think of your home network like a fancy restaurant. In the old days, once someone got past the front door (your WiFi password), they could go anywhere. Zero trust is like having a super-vigilant maitre d’ who checks everyone’s ID at every single door. Every device, every user, every single time.
You know what’s wild? Most home networks still use the same security model from the 1990s! Yikes! We’re living in 2025, folks – it’s time for an upgrade. Zero trust isn’t just some fancy corporate buzzword anymore. With more of us working from home and having dozens of connected devices, it’s becoming as essential as having locks on your doors.
I remember when one of my students asked me, “But isn’t this overkill for a home network?” Let me tell you what I told her: in today’s world, there’s no such thing as being too secure. Especially when you’re storing sensitive work documents, family photos, and financial information on your network. Plus, with all these smart devices, your home network knows more about you than your best friend does!
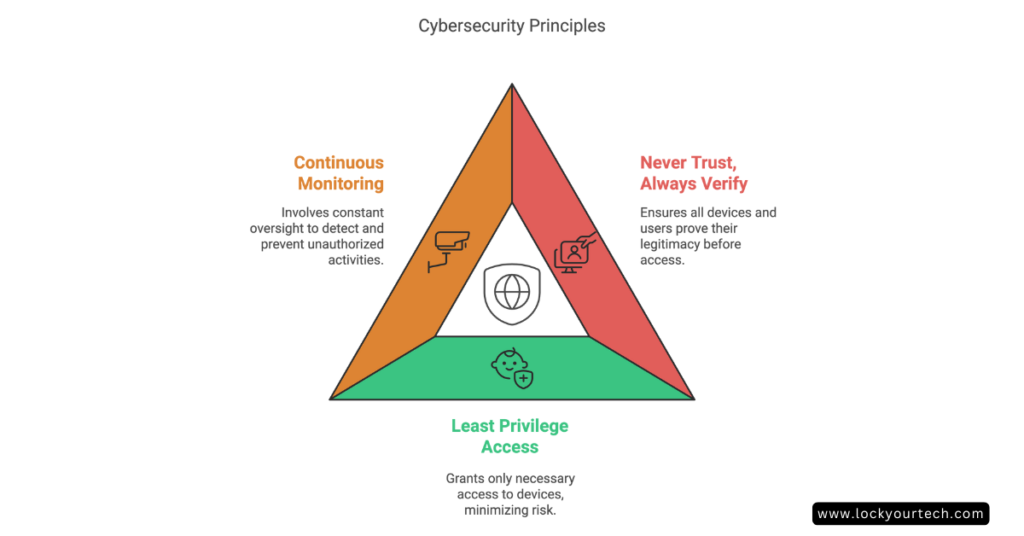
Core Zero Trust Principles
Let’s break down the core principles of zero trust in a way that won’t make your head spin. Think of it like teaching your kids about stranger danger, but for your devices!
First up is my favorite principle: Never Trust, Always Verify. I know it sounds a bit paranoid, but hear me out! Every single device and user needs to prove they’re legit – even your smart coffee maker. Last week, my “smart” doorbell tried accessing my personal files. Seriously, why does a doorbell need to know what’s in my tax returns folder?
Then we’ve got Least Privilege Access. This is like giving your kids an allowance – they get exactly what they need, nothing more. Your smart TV doesn’t need access to your work documents any more than your toaster needs to know about your banking information. Mind-blowing, right?
The last principle is Continuous Monitoring. Think of it as having a security camera that never sleeps. I set this up after noticing my network traffic spiking at 3 AM – turns out my “smart” fridge was having a late-night chat with servers in another country! Not on my watch, sneaky fridge!
These principles might sound complicated, but I promise you they’re not. Once you understand them, everything else falls into place. It’s like learning to ride a bike – seems impossible at first, but soon becomes second nature.
Essential Components of a Zero Trust Home Network
Let me share something that happened last month. My neighbor called me in a panic because someone had hacked their baby monitor. Why? Because it was on the same network as everything else! That’s when I helped them set up these essential components that every zero trust network needs.
First up is Network Segmentation – think of it like having different rooms in your house. You wouldn’t keep your valuable jewelry in the guest bathroom, right? Similarly, your work laptop shouldn’t hang out in the same “room” as your smart doorbell. I use VLANs (Virtual Local Area Networks) to create these separate spaces. It’s not as complicated as it sounds – most modern routers can handle this!
Next comes Identity Management. This is like having a really good bouncer at a club who remembers everyone’s face. Every device needs a secure identity – not just a simple username and password. I use something called MFA (Multi-Factor Authentication) wherever possible. Yes, it’s slightly annoying to pull out your phone for a code, but so is having your bank account emptied by hackers!
Last but definitely not least is Continuous Monitoring. I can’t tell you how many times this has saved my bacon! Just last week, my monitoring system caught my kid’s gaming console trying to access my home office network segment. Nice try, kiddo!
Here’s a pro tip I learned the hard way: always include Backup Systems. It’s like having a spare key to your house – you hope you never need it, but you’re really glad you have it when you do! I recommend a 3-2-1 backup strategy: three copies of your data, on two different types of media, with one copy off-site.
Step-by-Step Implementation Guide
Alright, let’s roll up our sleeves and get our hands dirty! Don’t worry if you’re not a tech wizard – I’ll walk you through this like I’m explaining it to my mom (who, by the way, now has a more secure network than most small businesses!).
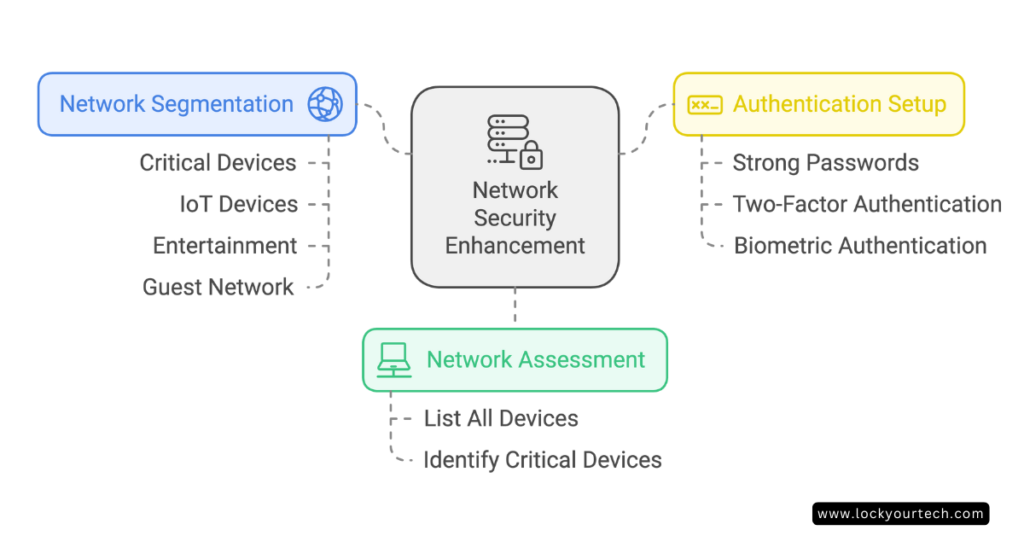
Step 1: Network Assessment
Start by making a list of EVERY connected device in your home. And I mean everything – even that ancient printer in the corner! I found 43 devices in my home when I first did this. Shocked face emoji!
Step 2: Network Segmentation Setup
This is where the magic happens! Create separate network zones for:
- Critical devices (work laptops, financial stuff)
- IoT devices (smart bulbs, thermostats)
- Entertainment (gaming consoles, smart TVs)
- Guest network (because your neighbor doesn’t need access to your printer)
Step 3: Authentication Setup
Remember that password you’ve been using since college? Time to say goodbye! Set up:
- Strong unique passwords (I use a password manager)
- Two-factor authentication wherever possible
- Biometric authentication when available
The key here is to take it slow and steady. Rome wasn’t built in a day, and neither is a secure home network. I usually tell my students to tackle one category of devices each weekend. This way, you won’t get overwhelmed, and you can make sure everything’s working properly before moving on
Legacy System Migration
You know what’s the biggest headache in my home network journey? Dealing with those old devices that just won’t die! Like my trusty printer from 2010 – it works perfectly fine, but it’s about as secure as a paper lock on a bank vault.
Here’s the deal with legacy systems: they’re like that old car you inherited from your grandpa – full of character but missing modern safety features. But don’t worry, I’ve got some tricks up my sleeve for handling these dinosaurs!
First, let’s talk about VPN Replacement. Those old-school VPNs are like using a sledgehammer to crack a nut – they get the job done, but at what cost? I recently switched to a ZTNA (Zero Trust Network Access) solution, and let me tell you, it’s like upgrading from a flip phone to a smartphone! Instead of giving access to everything, it only connects users to specific applications they need.
The key is taking baby steps. Start by:
- Identifying your legacy devices (anything older than 5 years is suspect)
- Creating a separate network segment just for these oldies
- Setting up strict access controls
- Monitoring them like a hawk
One thing I learned the hard way: don’t try to upgrade everything at once! When I did that, my smart home turned into a not-so-smart mess for a week. Take it slow, test everything, and have a backup plan.
Securing Different Device Categories
Let’s talk about the zoo of devices we all have at home. Each type needs its own special treatment – kind of like how you wouldn’t feed your cat dog food (trust me, I tried once… just kidding!).
Smart Home Devices
These are the trickiest ones because they’re often the least secure. I discovered my smart bulbs were chattier than a teenager – sending data every 30 seconds! Here’s what you need to do:
- Update firmware regularly (set a monthly reminder)
- Disable unnecessary features (does your thermostat really need Bluetooth?)
- Isolate them on their own network segment
Home Office Equipment
This is where I’m extra paranoid, and for good reason! Your work laptop is like the crown jewels of your network. Protect it with:
- Enterprise-grade antivirus software
- Regular security patches
- Separate network segment
- Strict access controls
Entertainment Systems
Gaming consoles and smart TVs are like gossiping neighbors – they love to share information! I caught my smart TV trying to connect to servers in five different countries in one day. Here’s how to keep them in check:
- Regular security audits
- Limited network access
- Content filtering
- Firmware updates
Remember that one time my gaming console tried to access my work files? Yeah, that’s not happening anymore! Every device category gets its own “playpen” with specific rules and boundaries.

Tools and Software Recommendations
Let me share my favorite tools that won’t break the bank. You don’t need to spend a fortune to secure your network – I learned this after wasting $500 on a “military-grade” router that wasn’t any better than my current setup!
Must-Have Security Tools:
First up is a good firewall. I use OPNsense on an old PC I had lying around. It’s free and works like a charm! If you’re not into DIY, the UniFi Dream Machine is worth every penny – it’s like having a security guard and network manager in one box.
For network monitoring, I swear by Wireshark (free) and Networx (budget-friendly). They’re like having x-ray vision for your network! I caught my neighbor’s kid trying to hack my WiFi using these tools – nice try, kiddo!
Here’s what I recommend for different budgets:
- Basic Setup ($100-200):
• Good quality router with VLAN support
• Network monitoring software (free options available)
• Basic firewall capabilities - Mid-Range Setup ($300-500):
• Dedicated firewall/router combo
• Network-wide antivirus
• Advanced monitoring tools - Pro Setup ($500+):
• Enterprise-grade equipment
• Professional monitoring solutions
• Automated backup systems
Remember when I mentioned my student who secured their entire network for under $200? They used:
- EdgeRouter X ($60)
- TP-Link access points ($40 each)
- Free monitoring tools
- Open-source security software
Maintenance and Monitoring
Alright, here’s the part most people skip – but it’s as crucial as changing your car’s oil! A secure network isn’t a “set it and forget it” deal. Trust me, I learned this the hard way when my “perfectly secure” network got breached because I forgot to update my router’s firmware for six months. Facepalm moment!
Here’s my monthly security checklist that keeps everything running smoothly:
Weekly Tasks:
- Check for unauthorized devices (I once found a mysterious device named “FBI Van” – turned out to be my teenager’s joke)
- Review access logs (boring but necessary!)
- Update any flagged security issues
Monthly Tasks:
- Full network scan
- Firmware updates for ALL devices
- Security policy review
- Backup verification
Quarterly Tasks:
- Complete security audit
- Password rotation
- Access permission updates
- Performance optimization
The key is to make it a routine. I do my network checks every Sunday morning with my coffee – it’s become almost meditative! Set reminders on your phone, and don’t skip them. One missed update could be the difference between a secure network and a hacker’s playground.
Pro tip: Keep a network journal. Note down any changes, updates, or weird behavior you notice. It’s like having a security camera for your network’s history. When something goes wrong (and trust me, something will eventually go wrong), you’ll thank yourself for keeping these records!
Conclusion
Creating a zero trust home network might seem daunting, but it’s an investment in your digital safety that pays off immensely. Start with the basics – assess your current setup, implement proper segmentation, and gradually build up your security measures. Remember, in today’s connected world, your home network’s security is only as strong as its weakest link.
Begin with a simple network audit and work your way through this guide. Your future self will thank you for taking action today!



